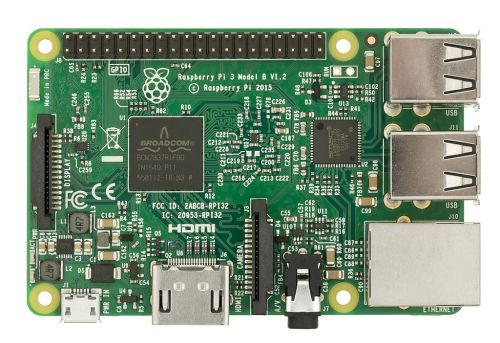
This weekend’s geeky challenge: Making a Raspberry Pi Security Camera. TL;DR – Here’s a basic, practically-ready-to-deploy, open-source Raspberry Pi security camera. Brief Mostly because I’m cheap (but partly to reduce the scope and therefore increase chance of success) I added a few constraints: Periodic still image capture is OK (streaming Continue Reading
Running an ASP.NET Core 2.0 app on Raspbian Stretch Linux on a Raspberry Pi with HTTPS
Today’s challenge: Serve a public API over HTTPS from a Raspberry Pi. I’ll follow up with an article about containerising the app and running it from docker on the Pi. This article is a fast-paced guide to getting started without stopping to dwell on the details. Some details will be Continue Reading